MOVEit Hack: The Solution That Could've Prevented It
Say Hello to the largest hack of 2023 - MOVEit, one of the largest file transfer services has been hacked.
Thousands of organizations worldwide use MOVEit’s file transfer service, to transfer large amounts of often-sensitive data over the Internet.
Let’s take a look at the MOVEit mass hack by the numbers:
- 60,144,069 individuals in total were affected
- + 2,500 organizations’ data compromised
- 11 million individual sensitive health information (including SSN)
- $9.9 Billion total cost (so far)
What Happened?
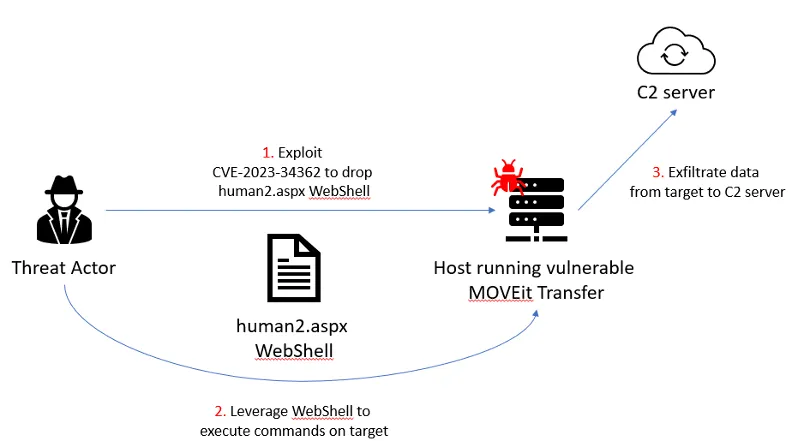
The MOVEit attack was a cyberattack that targeted a flaw in the MOVEit managed file transfer service. The attack was executed on May 27, 2023, and exploited a zero-day vulnerability to inject SQL commands and gain access to MOVEit customers' databases.
Three critical vulnerabilities have been confirmed by the owner company, Progress, (CVE-2023-34362, CVE-2023-35036, CVE-2023-35708), this could enable malicious entities to gain elevated rights and unauthorized entry into MOVEit’s environments.
Endless Number of MoveIT Victims
Months on, the number of victims keeps rising, although it's probable that the majority were compromised during the initial days and weeks of the campaign. The wide range of entities affected underscores the widespread difficulty of implementing timely software updates. Some of the most prominent include:
- BORN Ontario, which said data on 3.4 million locals over a 10-year period was compromised.
- French unemployment agency Pôle Emploi (10 million individuals impacted)
- Louisiana Office of Motor Vehicles (six million)
- Colorado Department of Health Care Policy and Financing (four million)
- Oregon Department of Transportation (3.5 million)
- The United States government has confirmed that several federal agencies have also fallen victim to attacks linked to the MOVEit Transfer vulnerability, with two critical infrastructure entities likely to be included in this list.
How TransferChain could help?
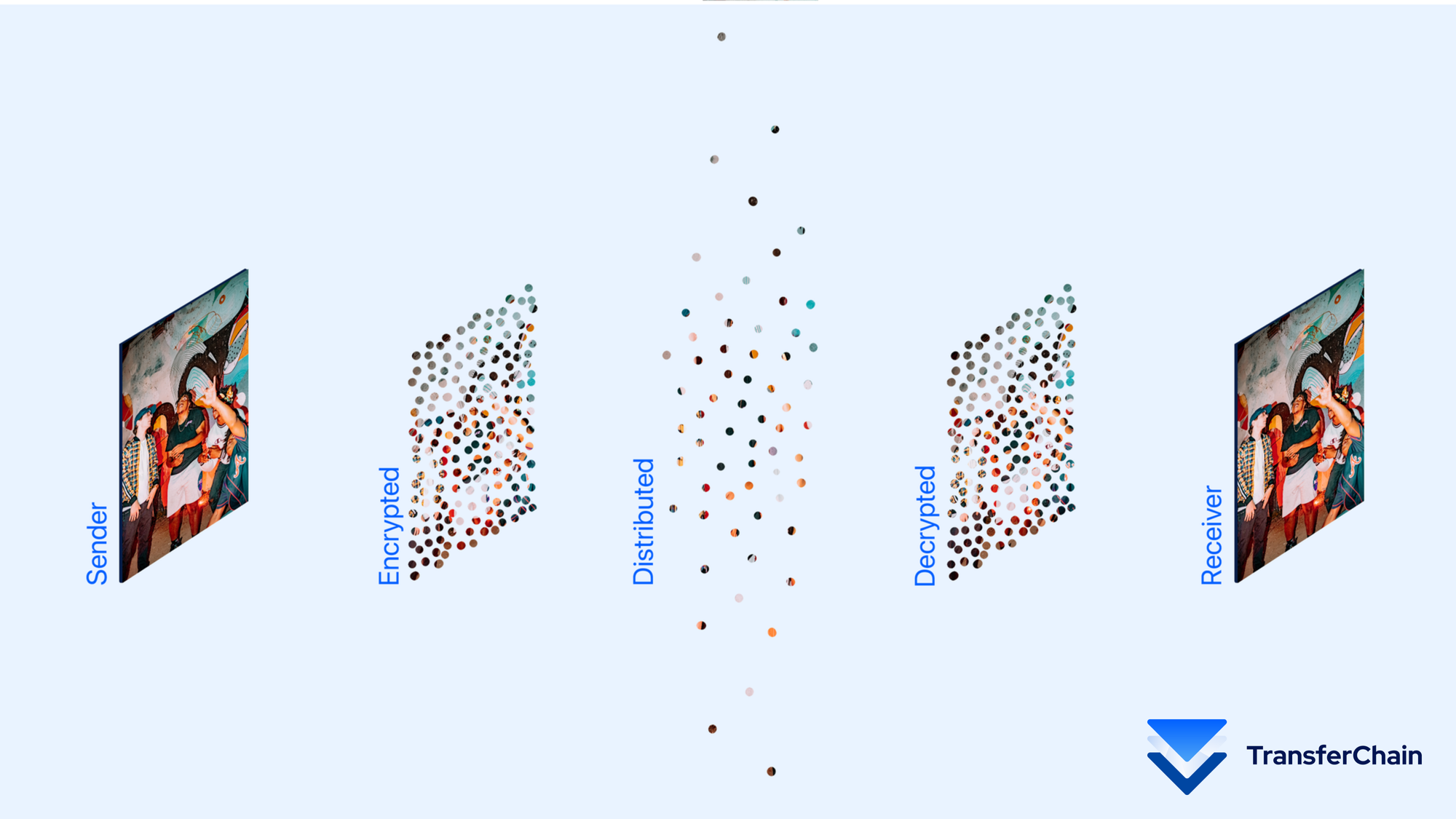
- Blockchain-Based Security: TransferChain utilizes blockchain to authorize every file transfer. All of the metadata regarding each transaction is only stored in the blockchain. Preventing any alteration from external users.
- Client-side and End-to-end Encryption: All of your files are client-side end-to-end encrypted using private keys that only you have access to; there are no centralized entities that store your keys or passwords.
- File fragmentation: each file is split into pieces after it is encrypted.
- Distributed cloud: Encrypted chunks are distributed to the safest storage providers in a randomized structure. Eliminating single point-of-failures.
- Zero trust architecture: A crucial part of the Zero Trust model is dividing your network into smaller, isolated segments (microsegments). If a hacker exploits a vulnerable software component, they will likely only have access to that specific network microsegment.
- Zero-knowledge structure: There is no point in time when any data is visible to unauthorized users or servers.
The MOVEit hack highlights the urgent need for cutting-edge cybersecurity solutions while also serving as a sobering reminder of the constantly changing nature of cyber threats. Clearly, today’s time requires a shift from legacy solutions to advanced solutions that incorporate data security and privacy measures for today and tomorrow.
At TransferChain, no one but you or the intended recipient can access your organization’s sensitive data.
With the growing dependence of both businesses and individuals on digital platforms, it’s clear that cutting-edge security solutions like TransferChain are not just optional; they are essential.
Ready to experience full security?
Start securing your privacy when sharing files now! 🔽
